Citrix Content Collaboration single sign-on configuration guide for Citrix Gateway
You can configure Citrix Gateway ADC using the Citrix ADC AAA feature to function as a SAML identity provider.
In this configuration, a user signing in to Citrix Content Collaboration using a web browser or other Citrix Files clients is redirected to a virtual server on Citrix Gateway with a SAML IP policy enabled for user authentication. After successful authentication using Citrix Gateway, the user receives a SAML token that is valid to sign in to their Citrix Content Collaboration account.
The configuration is required for the SP certificate to be created so it can be imported on Citrix Gateway and bind it to your Citrix ADC AAA virtual server. It is assumed for the purposes of this document that you have already created the appropriate external and internal DNS entries to route authentication requests that Citrix Gateway listens on, and that an SSL certificate has already been created and installed on Citrix Gateway for the SSL/HTTPS communication.
Configure Citrix Content Collaboration
- Sign in to your account at
https://subdomain.sharefile.comwith a user account that has admin rights. - Select Settings > Admin Settings.
- Select Security > Login & Security Policy, scroll down and select the Single Sign-On Configuration option.
- Under Basic Settings, check Enable SAML.
- In the ShareFile Issuer / Entity ID field enter:
https://subdomain.sharefile.com/saml/acs - In the Login URL field, enter the URL that users are redirected to when using SAML. Example:
https://aaavip.mycompany.com/saml/login - In the Logout URL field, enter the logout URL that expires the users’ session upon selecting the logout option in the web UI. Example:
https://aaavip.mycompany.com/cgi/tmlogout - For the X.509 Certificate, you must export the SSL certificate from your Citrix Gateway appliance that is going to be answering for your Citrix ADC AAA traffic. In the example above, this is referenced as being assigned the following FQDN:
aaavip.mycompany.com.
Follow the below steps to export this certificate.
- Sign in to your Citrix Gateway appliance using the Configuration Utility.
- Select Traffic Management > SSL.
-
On the right, underneath Tools, select Manage Certificates / Keys/ CSRs.
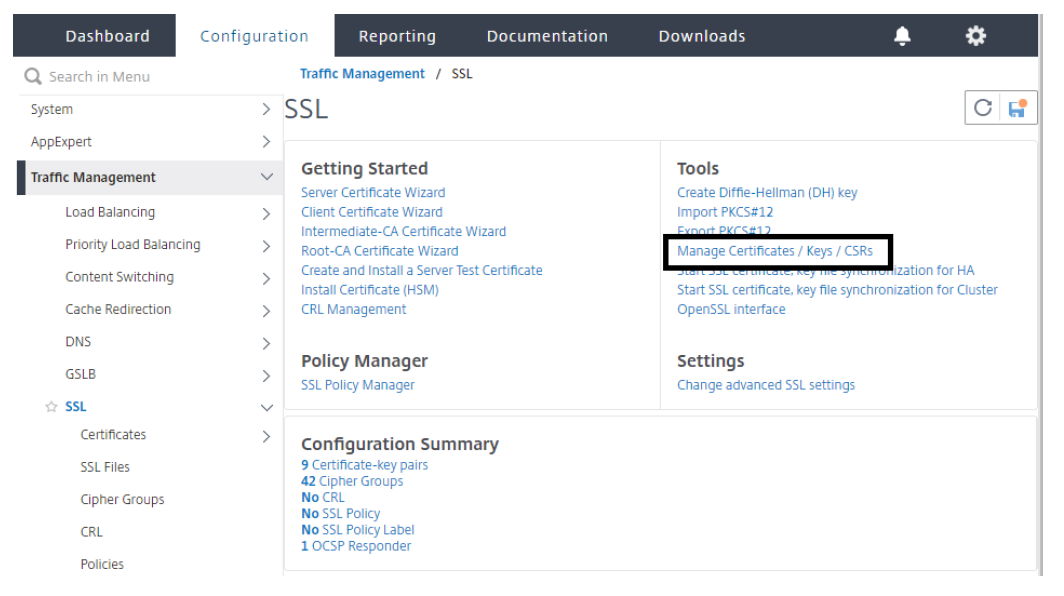
- From the Manage Certificates window, browse to the certificate you are using for your Citrix ADC AAA virtual server. Select the certificate and choose the Download button. Save the certificate to a location of your choice.
- From the downloaded location, right-click on the certificate and open it with a text editor such as Notepad.
- Copy the entire contents of the certificate to your clipboard.
- Navigate back to your Citrix Content Collaboration account using the web browser.
-
For the X.509 Certificate, select Change. Paste the contents of the certificate you copied to your clipboard into the window.
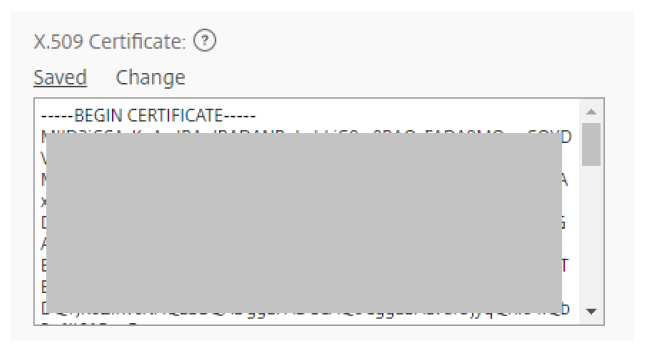
-
Select Save.
- Under Optional Settings, switch Require SSO Login to yes if you want all employee users to be required to use their AD credentials to sign in.
- Select the list next to SP-Initiated SSO Certificate. From the list, select HTTP Post (2048 bit certificate).
- Check Yes to force the SP-Initiated SSO Certificate to regenerate.
- Check Yes to Enable Web Authentication.
-
Under SP-Initiated Auth Context, choose Unspecified.
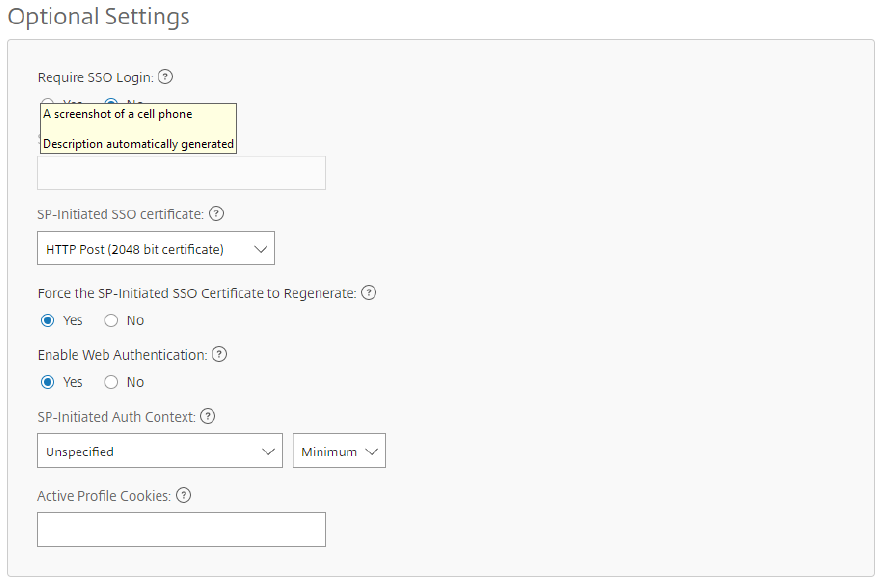
- Select the Save button at the bottom of the screen.
Configure Citrix Gateway
The following configuration is required for support as a SAML identity provider:
- LDAP Authentication Policy and Server for domain authentication
- SSL Certificate with External / Internal DNS configured accordingly to the FQDN being presented by the certificate (Wildcard certificates are supported)
- ShareFile SP Certificate
- SAML IdP Policy and Profile
- Citrix ADC AAA Virtual Server
For the purposes of this material, we cover the LDAP configuration, the ShareFile SP Certificate importation on Citrix Gateway, the SAML IDP settings, and the Citrix ADC AAA Virtual Server configuration. The SSL Certificate and DNS configurations must be in place prior to setup.
To configure domain authentication
For domain users to be able to sign in using their corporate email address, you must configure an LDAP Authentication Server and Policy on Citrix Gateway and bind it to your Citrix ADC AAA VIP. Use of an existing LDAP configuration is also supported.
- In the configuration utility, select Security > AAA – Application Traffic > Policies > Authentication > Basic Policies > Policy > LDAP in the left navigation pane.
- To create an LDAP policy, on the Policies tab, click Add… and then enter ShareFile_LDAP_SSO_Policy as the name. In the Action Type, select LDAP.
- In the Action field, click + to add a server. The Create Authentication LDAP Server window appears.
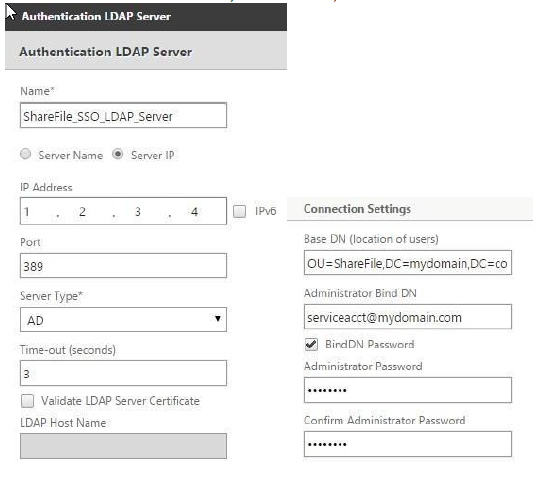
- In the Name field, enter ShareFile_LDAP_SSO_Server.
- Select the bullet for Server IP. Enter the IP address of one of your AD domain controllers. You can also point to a virtual server IP for redundancy if you are load-balancing DCs.
- Specify the port that the NSIP uses to communicate with the domain controller. Use 389 for LDAP or 636 for Secure LDAP.
- Under Connection Settings, enter the Base DN where the user accounts reside in AD that you would like to allow authentication. Ex. OU=ShareFile,DC=domain,DC=com.
- In the Administrator Bind DN field, add a domain account (using an email address for ease of configuration) that has rights to browse the AD tree. A service account is advisable such that there are no issues with sign-ins if the account that is configured has a password expiration.
- Check the box for Bind DN Password and supply the password twice.
- Under Other Settings, enter sAMAccountName as the Server Logon Name Attribute.
- Under the Group Attribute field, enter memberof.
- Under the Sub Attribute field, enter CN.
- Click More.
- Scroll down and in the Attribute Fields, Attribute 1, enter mail.
- Click the Create button to complete the LDAP server settings.
- For the LDAP Policy Configuration, select the newly created LDAP server from the server menu, and in the Expression field, type true.
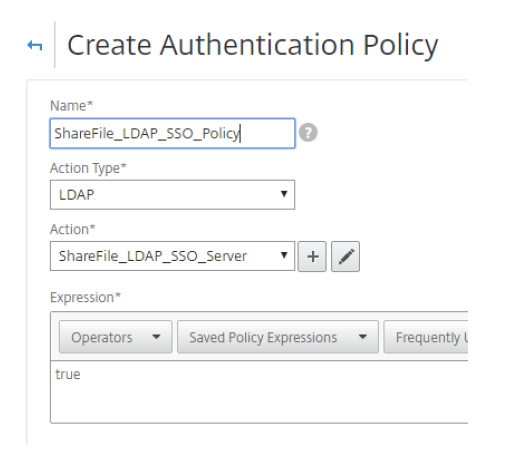
Click Create to complete the LDAP policy and server configuration.
To import the SP-Certificate onto Citrix Gateway
- Sign in to your account at
https://subdomain.sharefile.comwith a user account that has admin rights. - Select the Settings > Admin Settings link near the left/center of the page. Select Security > Logon & Security Policy, then scroll down to Single Sign-On Configuration.
- Under Optional Settings, next to SP-Initiated SSO Certificate, HTTP Post (2048 Bit Certificate) click View.
- Copy the entire certificate hash to your clipboard and paste it into a text reader such as Notepad.
- Observe the formatting and remove any extra spaces or carriage returns at the end of the file, then save the text file as ShareFile_SAML.cer.
- Navigate to the Citrix Gateway configuration utility.
- Select Traffic Management > SSL > Certificates > CA Certificates.
- Click Install.
- From the Install Certificate window, provide a Certificate-Key Pair Name.
- Under the Certificate File Name section, select the menu next to Browse and select Local. Browse to the location you saved the ShareFile_SAML.cer file.
- Once the file is chosen, select Install.
To configure the SAML IdP policy and profile
For your users to receive the SAML token to sign in to Citrix Content Collaboration, you must configure a SAML IdP policy and profile, which is bound to the Citrix ADC AAA virtual server that the users are providing their credentials to.
The following steps outline this process:
- Open the Citrix Gateway configuration utility and navigate to Security > AAA – Application Traffic > Policies > Authentication > Advanced Policies > SAML IDP.
- Under the Policies tab, select the Add button.
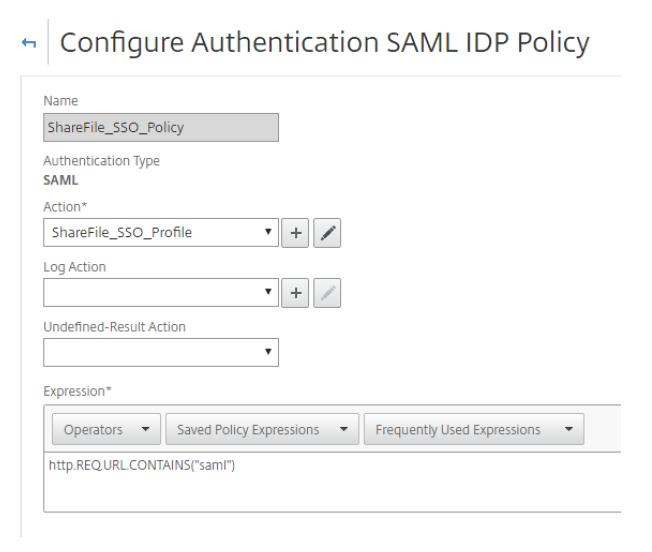
- From the Create Authentication SAML IDP Policy window, provide a name for your policy, such as ShareFile_SSO_Policy.
- To the right of the Action field, select the + sign to Add a new Action/Profile.
- Provide a name such as ShareFile_SSO_Profile and remove the check box for Import Metadata. If you are running an older version of NetScaler, this check box might not exist.
- In the Assertion Consumer Service URL field, enter your Citrix Content Collaboration account URL followed by /saml/acs:
Ex. https://subdomain.sharefile.com/saml/acs - In the IDP Certificate Name field, browse to the certificate installed on Citrix Gateway that is used to secure your Citrix ADC AAA authentication virtual server.
- In the SP Certificate Name field, select the menu and browse to the SP certificate you imported earlier and added as a CA certificate.
- For Sign Assertion, leave ASSERTION.
- Clear Send Password.
- In the Issuer Name field, enter the URL for your Citrix ADC AAA traffic. Example –
https://aaavip.mycompany.com. - Leave Service Provider ID blank.
- Clear Reject Unsigned Requests.
- Signature Algorithm, RSA-SHA256
- Digest Method, SHA256.
- For SAML Binding, select POST.
- Click More.
- Under the Audience field provide the URL for your Citrix Content Collaboration account.
- For Skew Time, enter 5. This allows for a 5 minute time difference between the client, Citrix Gateway, and Citrix Content Collaboration.
- For Name ID Format, select Transient.
-
In the Name ID Expression field, type the following:
aaa.user.attribute(1). If using NetScaler 11.x, typehttp.req.user.attribute(1).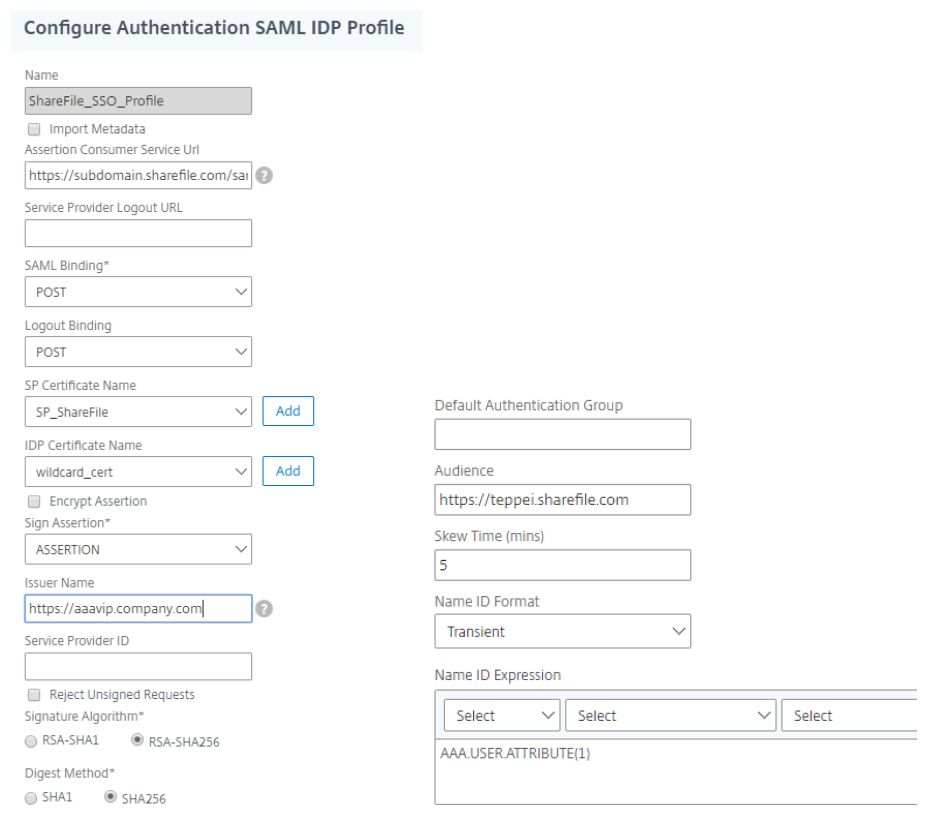
- Click Create to complete the SAML IdP profile configuration and return to the SAML IdP Policy creation window.
- In the Expression field, add the following expression:
HTTP.REQ.URL.CONTAINS(“saml”) -
Click Create to complete the SAML IdP configuration.
To configure your Citrix ADC AAA virtual server
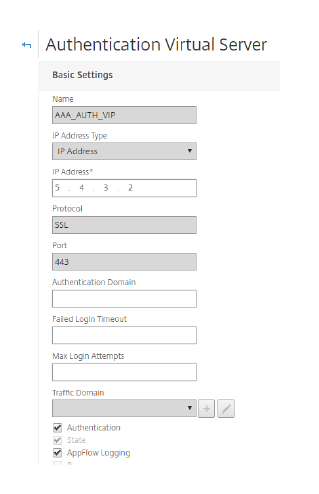
When an employee attempts to sign in, for them to utilize their corporate credentials, they are redirected to a Citrix Gateway Citrix ADC AAA Virtual Server. This virtual server listens on port 443, which requires an SSL certificate, in addition to external and internal DNS resolution to the IP address being hosted on Citrix Gateway. The following steps require these pre-exist, assume that the DNS name resolution is already in place, and that the SSL certificate is already installed on your Citrix Gateway appliance.
- In the Configuration Utility, navigate to Security > AAA – Application Traffic > Virtual Servers and select the Add button.
- From the Authentication Virtual Server window, provide a name and an IP address.
-
Scroll down and make sure that the Authentication and State check boxes are checked
- Click Continue.
- In the Certificates section, click No Server Certificate.
- From the Server Cert Key window, click Bind.
- Under SSL Certificates, choose your Citrix ADC AAA SSL Certificate and select Insert. Note: This is NOT the ShareFile SP certificate
- Click Bind, then click Continue.
- From the Advanced Authentication Policies option, click No Authentication Policy.
- From the Policy Binding page, select Policy, select ShareFile_LDAP_SSO_Policy created earlier.
- Click Select, then Bind (leaving defaults) to return to the Authentication Virtual Server screen.
- Under Advanced Authentication Policies, click No SAML IDP Policy.
- Under Policies, select your SHAREFILE_SSO_POLICY. Click Select.
- From the Policy Binding page (leave defaults), click Bind, then Close.
- Click Continue and Done.
Validate the configuration
- Go to
https://subdomain.sharefile.com/saml/login. You are now redirected to the Citrix Gateway sign-in form. - Sign in with your user credentials that are valid for the environment you configured. Your folders at
subdomain.sharefile.comnow appear.