This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica.(Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています.免責事項
이 기사는 기계 번역되었습니다.책임 부인
Este artigo foi traduzido automaticamente.(Aviso legal)
这篇文章已经过机器翻译.放弃
Questo articolo è stato tradotto automaticamente.(Esclusione di responsabilità))
Translation failed!
Threat detection alerts
If ShareFile detects unusual account activity, it will send out an email alert so admins, employee users, or client users of ShareFile can act on threats as soon as they’re detected.
Security alerts and recipients
Security alerts are sent to each persona in the given scenarios. To view/change current security alert preferences, please refer this page
| Alert type | Client / Employee | Account Owner | Folder owner |
|---|---|---|---|
| Unusual location alert | Y | Y | Y |
| Unusual device & location alert | Y | Y | Y |
| More than 5 failed sign-in attempts | Y | Y | |
| Malware upload | Y | Y |
-
Client / Employees - refers to the client and employee users who access ShareFile accounts.
-
Account Owner - The account owner is the primary administrator with the highest level of permissions, granting them the ability to authorize account-wide settings and delegate privileges to other administrators. There is only one account owner per ShareFile account.
-
Folder owner - refers to the employees or users with access to ShareFile accounts.
The security alert dashboard includes:
-
Alert History - A log of the past 30 days threats and their details, allowing users to review historical security events.
-
Event Timeline - A chronological list of activities and events related to the alert, providing context about what happened.
-
Affected Files or Folders - Information about the specific files or folders that may have been involved in the security event.
-
User and Location Details - Details about the user accounts, devices, and locations associated with the alert.
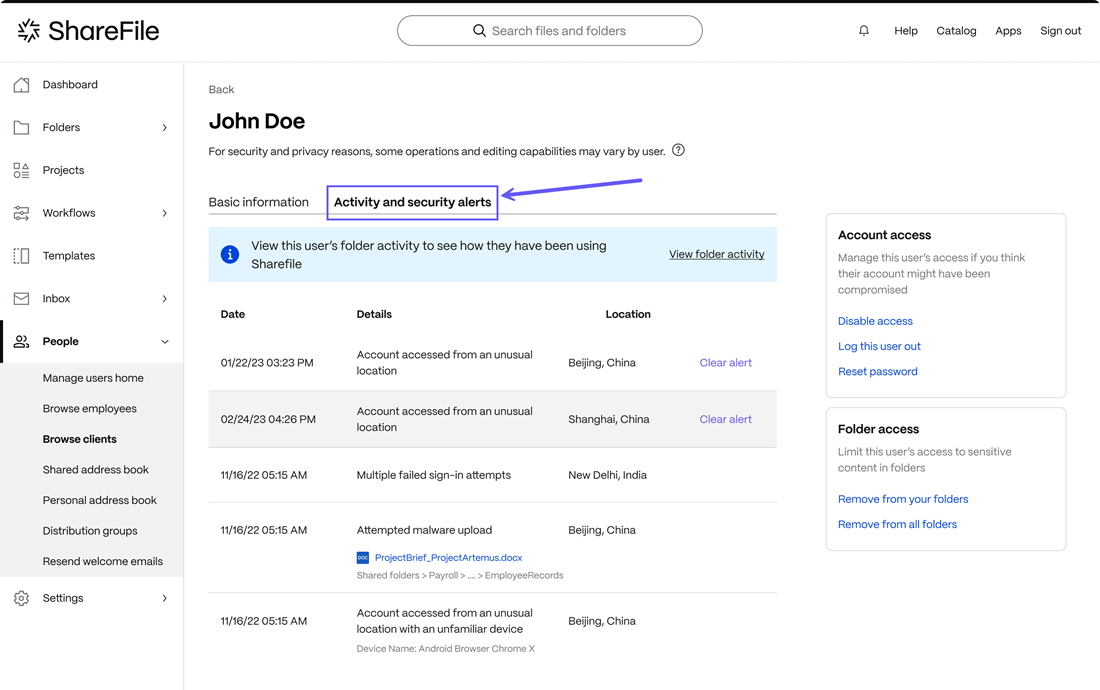
Employees and administrators can access the Activity and Security Alerts dashboard within the ShareFile web UI by navigating People > Browse client contacts > select client name then selecting the Activity and Security Alerts tab that provides detailed information about the alert.
NOTE:
Once a security alert is generated and added to the alert logs, it cannot be manually removed by administrators or users. If an alert is flagged in error, admins can’t remove the flag manually and must wait for it to clear automatically after 30 days.
Activity and Security Alerts dashboard
The ShareFile Activity and Security Alerts dashboard provides a view of recent security alerts and user activity details when a security warning occurs.
The security dashboard provides a range of response actions, allowing you to proactively mitigate potential risks. Users can review folder activity, users simply need to tap on the Review folder activity button. This opens a list of all folders allowing you to select the period of time using the drop-down list. The list includes the date, time, location, and the type of action.
Email alerts
These notifications are designed to keep you informed in real-time about any unusual activities or potential threats related to your data.
-
Upon receiving an alert notification email, select the Review user activity button to review the activity.
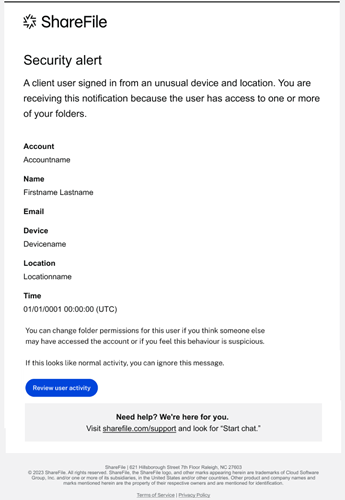
Selecting Review user activity redirects you to your dedicated security dashboard. The security dashboard serves as a central hub for comprehensive threat analysis and response.
-
Review the items listed under the Activity and Security Alerts tab.
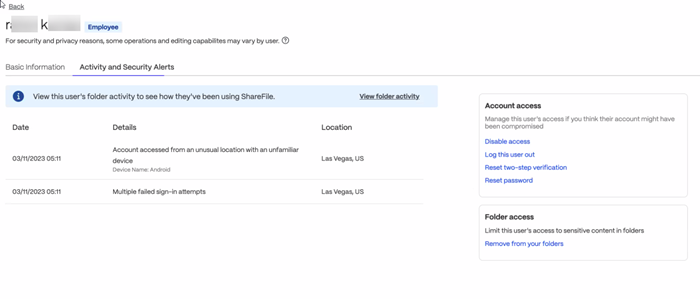
Within the security dashboard, you’ll have access to detailed threat information, including the nature of the alert, a chronological timeline of events, files and folder details, and specific user and location details.
Users can take actions like disabling other user’s access, resetting the user password, and removing from folder access.
Threat remediation
ShareFile offers several actions to mitigate threats. Once alerts are received, employees, clients, and administrators can use the information provided by the alerts to take action.
Roles and Actions:
Employee and client users: - upon receiving an alert can take immediate action including:
- Change Password If they receive an alert about unusual access or failed sign-in attempts, they can change their password to secure their account.
- Review Files If alerted about a malware upload, clients can review their files and delete them if necessary.
Administrators: - upon receiving a notification can take several steps to stop a threat including:
- Blocking account access Admins are able to disable access to an account and delete the user from the system.
- Limit folder access Admins can change permissions for folder access and review folder activity.
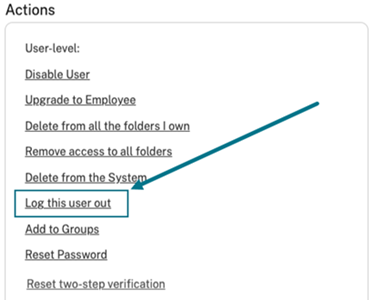
- Log the user out Admins can log a user out and reset the password or two-step verification.
- Review files Admins can review, delete, and quarantine the affected files.
Actions to take when an alert is received
-
Change your password: if you receive an alert of unusual access on your account, select Change Password to secure your account.
-
Manage Folder Permissions: if you receive an alert of unusual access on a user or client account, change the folder permissions. For more information on changing folder permissions, see Assigning folders and setting permissions.
-
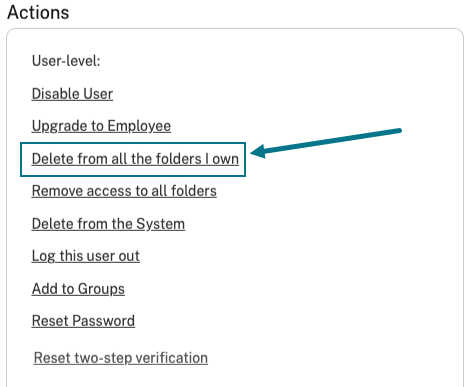
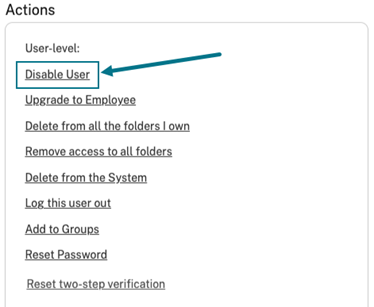
User specific actions: from your ShareFile account, navigate to People > then select between Browse Employees or Browse client contacts to perform the following actions if necessary:
-
Log this user out: if you receive an alert of unusual access on a user or client account, you can log the user out.
-
Delete from all the folders I own: if you receive an alert of unusual access on a user or client account, you can delete the user from all the folders you own.
-
Disable User: if you receive an alert of unusual access on a user or client account, you can disable the users account.
-
Manage notifications
NOTE:
Only the Account Owner can make changes to Security alert settings.
The ShareFile Account Owner is able to select what type of notification emails are sent to different account types. Administrators can tailor the notification settings to align the unique needs and responsibilities of each account.
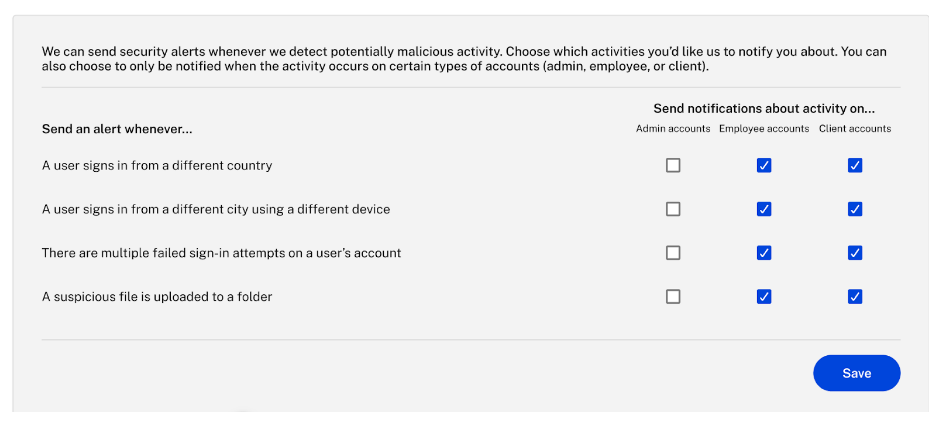
Enabling notifications by Admin
If an administrator enables notifications for employees, recipients will receive alert emails regardless of their individual settings. In this scenario, even if employees have disabled notifications, they will still receive alerts per the admin’s configuration.
Disabling Notifications by Admin
If an administrator chooses to disable notifications for clients, recipients will not receive alert emails. However, if individuals have enabled notifications for themselves, they will still receive alerts. Admin overrides do not affect individual user preferences in this case.
Mutual Disabling by Admin and Employees
When an administrator disables notifications for employees and individuals on their end and also disables notifications, no alert emails will be sent. This mutual agreement makes it a seamless experience without unnecessary alerts.
Flexible Email Notification System for Security Alerts
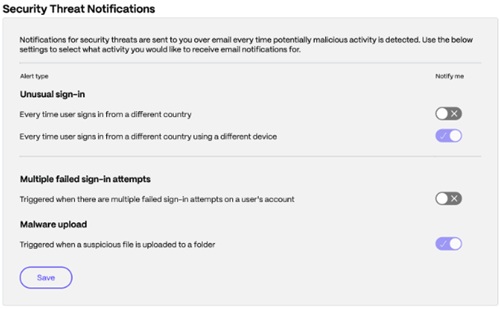
Employee users can tailor their email notifications to their preferences. This ensures they are informed about critical security incidents without being overwhelmed by less urgent alerts.
The following information defines the user email notification preferences for security alerts customization.
-
Individual control - Each employee user can customize their email notification preferences for security alerts. They can access their settings or preferences within the system to specify which types of security alerts they want to receive via email.
-
Enable and Disable alerts - Within their settings, employee users can enable or disable specific types of email notifications. For instance, they might choose to receive email alerts for critical security incidents but disable notifications for less severe issues.
Threat alerts forwarding to internal security teams
This allows Admins to efficiently route security-related email alerts to their organization’s internal security team. This ensures prompt action and effective communication in the face of potential threats.

Alert forwarding overview
-
Email routing setup - Admins can access the Alert Preferences section within ShareFile to enable the Email Alert Routing feature. Once activated, they can specify one or more email addresses for their internal security team or distribution list to receive security-related email alerts.
-
Customization Options - Users have the flexibility to add, edit, or remove email addresses associated with the internal security team as needed. Additionally, they can customize the feature by specifying multiple email addresses for different security teams or individuals within the organization.
-
Email Format and Call to Action - Recipients will receive alerts in the same format as Admin emails within the system, providing detailed information about specific security events. This fosters a cohesive and informed response to potential threats.
Improvise current threat alerting and removal of security icon
Overview
The Security Ticker is an alert indicator that appears next to an employee or client’s name when a security alert is triggered. This ticker helps users stay informed about potential security risks related to their account. Previously, these alerts remained visible until expiration, even after being reviewed. Now, admins can manually dismiss them, and they will auto-expire after 15 days if not acknowledged.
How to Remove the Security Ticker
Any ShareFile user with the “Manage Clients” / “Manage Employee” permission can remove the Security Ticker. To do so, simply click on the security alert icon and you will be automatically redirected to the Activity & Security Alerts tab, where you can review and manage alerts.
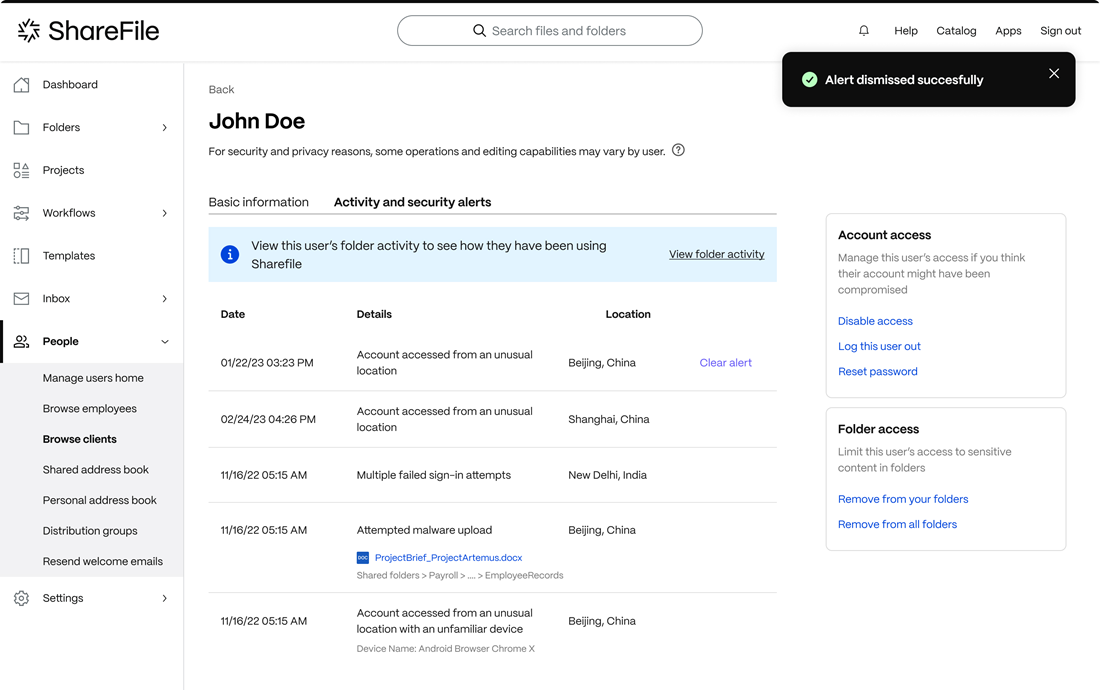
Manual Removal
Account owners and Employee Users with required permissions can remove security alerts manually:
- Login to ShareFile and navigate to the affected user’s profile.
- Select the Activity & Security Alerts tab.
- Browse and review all the listed security alerts.
- Select the alerts and mark them as reviewed as shown in the screenshot below..
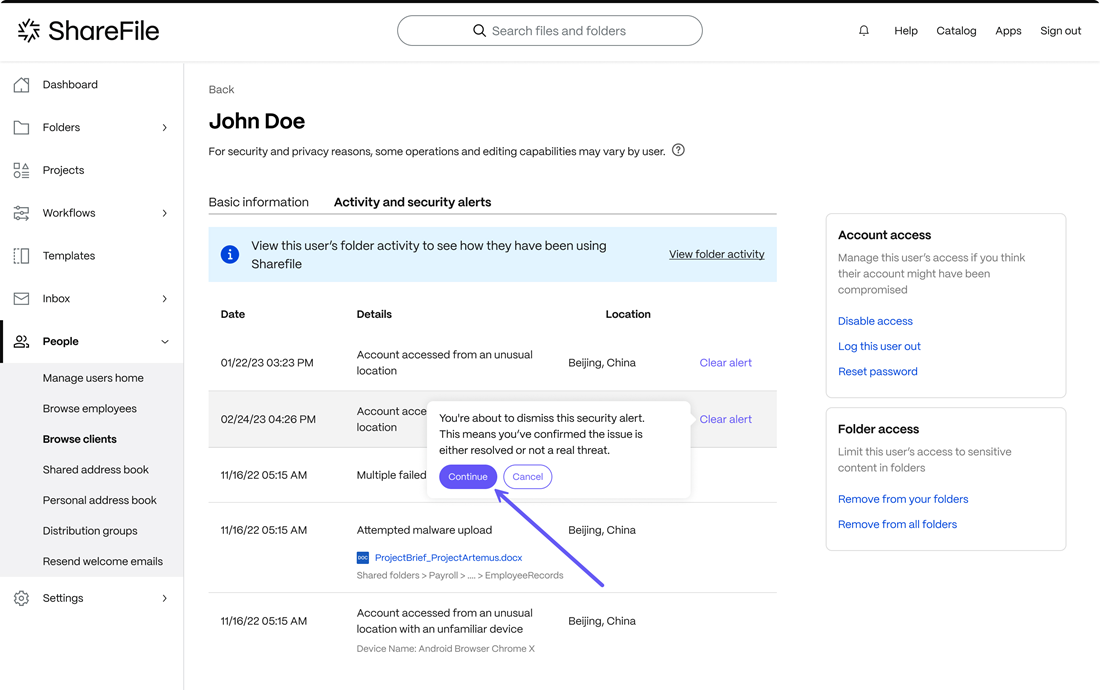
- The security ticker will disappear immediately from the user’s profile.
Automatic Removal
If alerts are not acknowledged or removed manually, the security ticker will automatically disappear after 15 days.
When users hover over the ticker, a tooltip will appear, guiding them to the Activity & Security Alerts tab for review and dismissal.
This feature ensures that security alerts remain visible only for the necessary duration, reducing clutter while maintaining security awareness.
ShareFile threat detection alerts FAQ
What are the threat detection alerts?
A threat detection alert is a notification that you receive when a potential security threat has been detected on your account or system. ShareFile sends alerts to keep your data and account safe.
Why am I getting these alerts?
Threat detection alerts are sent to help you protect your account and system from harm. By being aware of potential threats, you can take steps to mitigate them before they cause any damage.
The first thing to do is verify its legitimacy. Ensure that the emails are either from sharefile@sf-notifications.com or mail@sf-notifications.com.
You have to confirm that the alert is legitimate.
-
Client - Once the client receives an email, they can change the password.
-
Employee / owner - Once they receive an email, they can select the Review user activity tab within the email. You’re redirected to the dashboard, where you can take the appropriate action, depending on the nature of the threat from the dashboard.
What is the security dashboard? What actions can I take?
It’s where employees/admins can see all the alert details. It provides real-time insights into security events, threats, and vulnerabilities. Actions like disabling another user’s access, deleting the user, or resetting the user’s password are available.
What type of activities will I receive emails?
Clients, employee users, and administrators receive emails for the following types of suspicious activities:
- Unusual login from a different location
- Unusual login from different device and location
- Malware upload
- Multiple authentication failure
Share
Share
This Preview product documentation is Citrix Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Citrix Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Citrix product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.